Json Sql Injection Cheat Sheet
Hashtags will (yeah its no more number sign or pound key:( ) tell sql to ignore the rest so it will take it as right. User can also input (123' and '=' ) from the interface for username and your code would add final ' which would do the same affect with example above. Google sql injection cheat sheet and examples. For example a valid email address may contain a SQL injection attack or a valid URL. To defend formats such as JSON when possible. Mass Assignment Cheat Sheet.
About
The SQL Injection scan checks how your service handles incorrect or malicious SQL statements.
Typically, attackers try to use SQL injections in order to expose flaws in the web service security or obtain sensitive data. The SQL Injection scan simulates such requests, ensuring your server does not reveal any information that may be useful for further attacks.
If the scan does not reveal any information about possible vulnerabilities, it passes successfully.
If the scan has Failed, that may indicate your service is vulnerable to SQL attacks or cannot handle the authorization routines correctly.
Requirements
This scan is applicable to all types of test steps or requests.
How it works
The SQL Injection scan tries to attack the web service by replacing the original parameters of a test step with a malicious string, which exposes potential flaws in that service. The scan injects potentially harmful values to both XML elements and JSON fields.

This scan uses assertions to validate each response and check if it includes any information about potential vulnerabilities.
If a response passes all assertions, PASS will be logged for that response. If any assertion fails, FAIL will be logged.
If you have not applied any assertions to the scan, Unknown will be logged for the response. |
Assertions
Default Assertion
Sensitive Information Exposure – Verifies that your server does not reveal any information that is useful for attacks (such as stack traces if the server crashes).Recommended Assertion
Valid HTTP Status Codes – Verifies that the request does not return a5xxstatus code (a server error).
Parameters
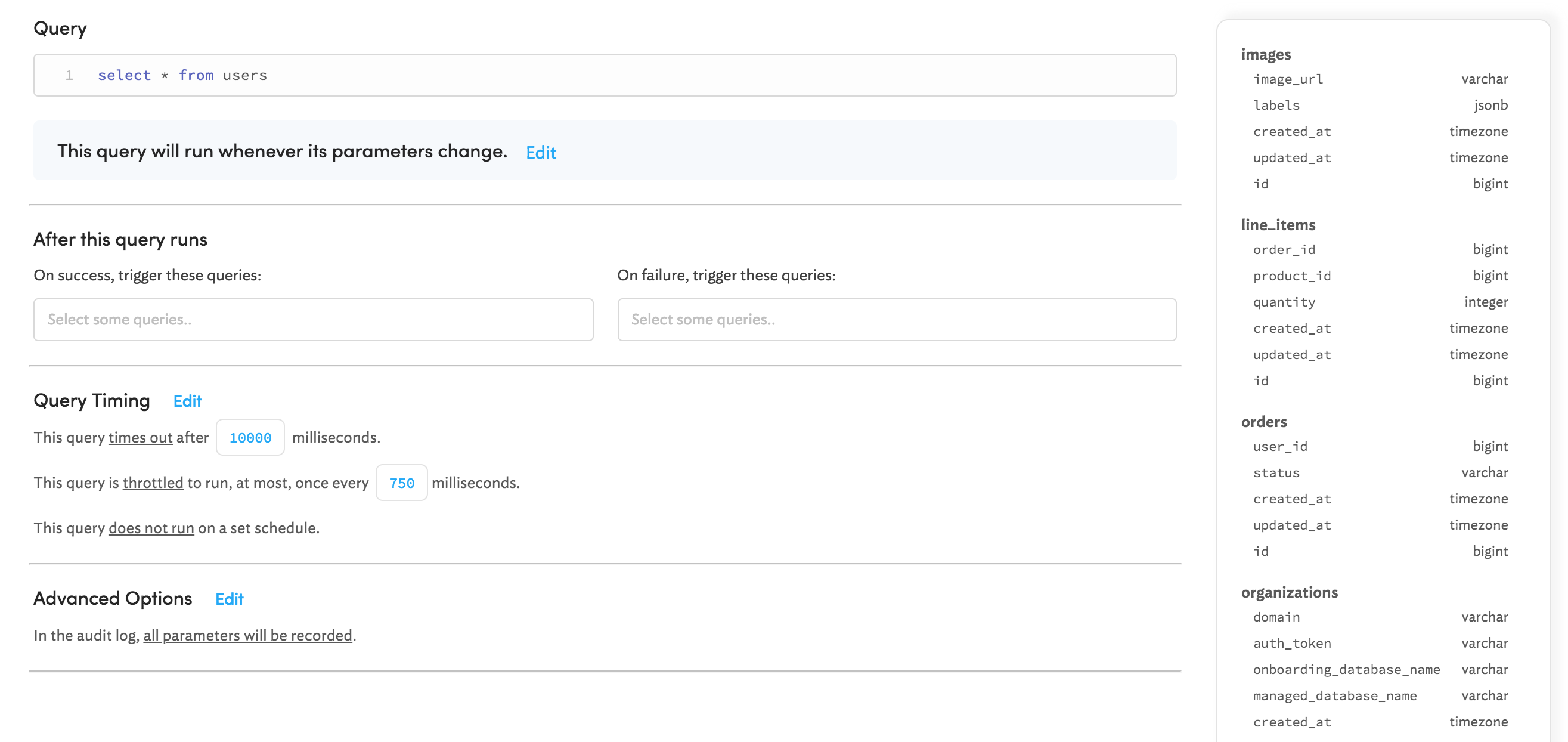
The SQL Injection scan inserts values into the message parameters of your SOAP or REST requests.
Normally, parameters are extracted automatically when you create the scan. If there are no parameters present, ReadyAPI will not run the SQL Injection scan. See Parameters for more information.
Use the following options to configure the scan Strategy:
| Option | Description |
|---|---|
| Select Strategy | One by One – Select to use requests one by one (may take some time). All At Once – Select to use all requests at once. |
| Request Delay (ms) | Set a pause between requests during the scan in milliseconds. |
| Apply to Failed TestSteps | Select to run the scan even if the target test step fails. |
| Run only once | Select to run the scan only once for each test step, even if ReadyAPI runs that step several times for a test case. |
On the Advanced panel, define values which the scan will insert into parameters.
| To... | Do the following... |
|---|---|
| Add one or more strings | Click and enter a list of strings in the Import Strings dialog. Click OK. Each line will appear as a separate string. |
| Replace all strings | Click and enter a new list of strings in the Import Strings dialog. Select Remove existing injection strings and click OK. Each line will appear as a separate string and all previous strings will be removed. |
| Edit a string | Select the line you want to edit and click . Specify the new value and click OK. |
| Delete a string | Select the line you want to delete and click . Confirm your choice. |
Related materials
SQL Injection Prevention Cheat Sheet on Open Web Application Security Project
SQL injection on the OWASP website
See Also
XPath Injection Scan
Sensitive Information Exposure Assertion
Valid HTTP Status Codes Assertion
Security Scans Types
Last revision (mm/dd/yy): 04/7/2018
- 1Introduction
- 1.1Client Side (Javascript)
- 1.2Server Side
- 1.2.2Protect against JSON Hijacking for Older Browsers
This document will provide a starting point for AJAX security and will hopefully be updated and expanded reasonably often to provide more detailed information about specific frameworks and technologies.
Client Side (Javascript)
Use .innerText instead of .innerHtml
The use of .innerText will prevent most XSS problems as it will automatically encode the text.
Don't use eval
Eval is evil, never use it. Needing to use eval usually indicates a problem in your design.
Canonicalize data to consumer (read: encode before use)
When using data to build HTML, script, CSS, XML, JSON, etc. make sure you take into account how that data must be presented in a literal sense to keep it's logical meaning. Data should be properly encoded before used in this manner to prevent injection style issues, and to make sure the logical meaning is preserved.
Don't rely on client logic for security
Least ye have forgotten the user controls the client side logic. I can use a number of browser plugging to set breakpoints, skip code, change values, etc. Never rely on client logic.
Don't rely on client business logic
Just like the security one, make sure any interesting business rules/logic is duplicated on the server side less a user bypass needed logic and do something silly, or worse, costly.
Avoid writing serialization code
This is hard and even a small mistake can cause large security issues. There are already a lot of frameworks to provide this functionality. Take a look at the JSON page for links.
Avoid building XML or JSON dynamically
Just like building HTML or SQL you will cause XML injection bugs, so stay way from this or at least use an encoding library or safe JSON or XML library to make attributes and element data safe.
Never transmit secrets to the client
Anything the client knows the user will also know, so keep all that secret stuff on the server please.
Don't perform encryption in client side code

Use TLS/SSL and encrypt on the server!
Postgresql Sql Injection Cheat Sheet
Don't perform security impacting logic on client side
This is the overall one that gets me out of trouble in case I missed something :)
Server Side
Json Sql Injection Cheat Sheet Pdf
Use CSRF Protection
Protect against JSON Hijacking for Older Browsers
Json Sql Injection Cheat Sheet Excel
Review AngularJS JSON Hijacking Defense Mechanism
See 'JSON Vulnerability Protection' from https://docs.angularjs.org/api/ng/service/$http
Always return JSON with an Object on the outside
Always have the outside primitive be an object for JSON strings:
Exploitable:
Not exploitable:
Also not exploitable:
Json Cheat Sheet Pdf
Avoid writing serialization code. Remember ref vs. value types!
Look for an existing library that has been reviewed.
Services can be called by users directly
Even though you only expect your AJAX client side code to call those services the users can too. Make sure you validate inputs and treat them like they are under user control (because they are!).
Avoid building XML or JSON by hand, use the framework
Use the framework and be safe, do it by hand and have security issues.
Use JSON And XML Schema for Webservices
You need to use a 3rd party library to validate web services.
Json Sql Injection Cheat Sheet Examples
Authors and Primary Editors
Til Mas
Michael Eddington
Other Cheatsheets
