2fa 1password
- Use 1password 2fa
- 2fa 1password Fortnite
- 1password 2fa Scanner Not Working
- 2fa 1password
- 2fa 1password Extension
- 1password 2fa Lost Phone
Two step authentication, 2-step Verification SMS code password concept. Smartphone with special 2FA software and tablet pc with multi-factor authentication safety and secure login form.
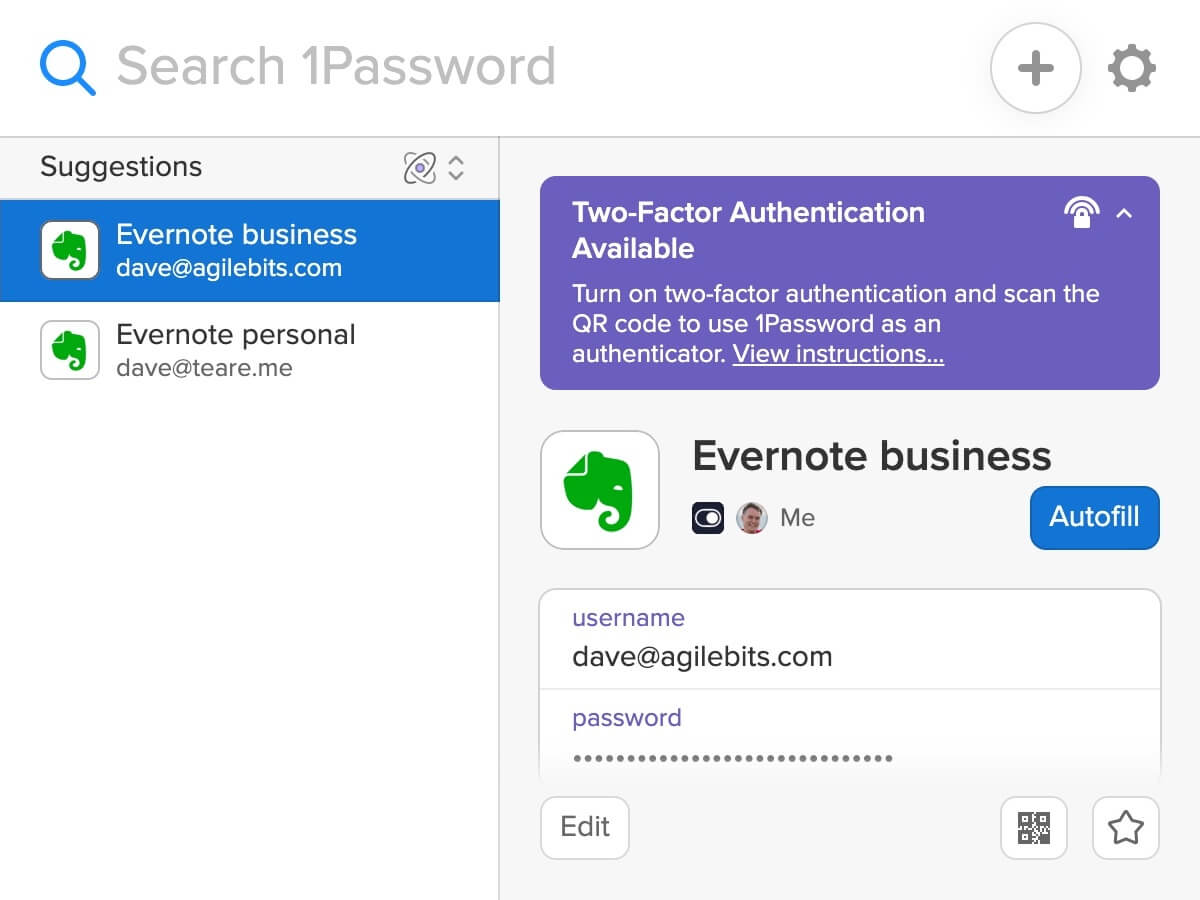
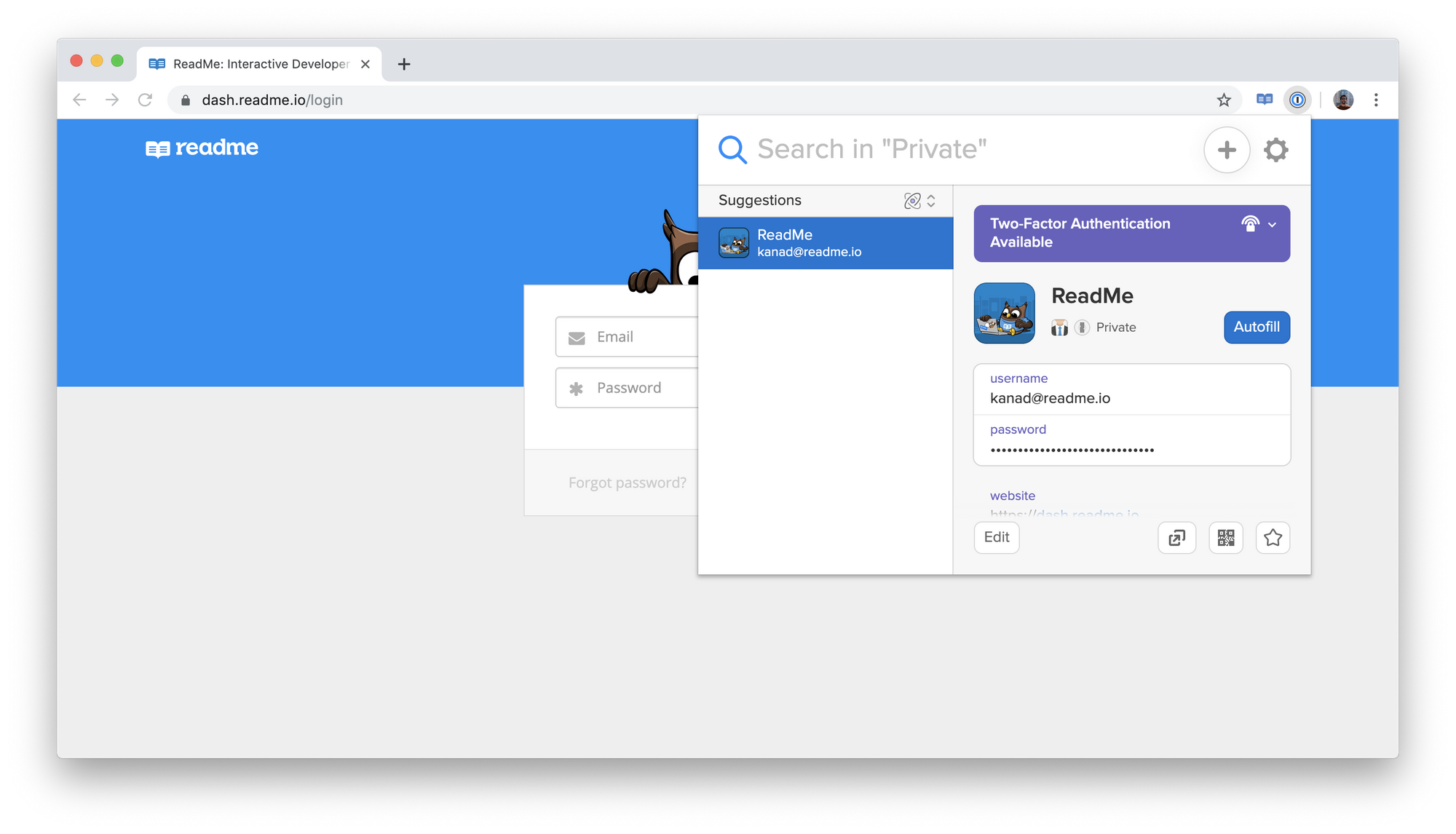
Adding 2FA Codes to 1Password After you follow 1Password’s link to enable 2FA on a site, that site will typically present you with a QR Code. If 1Password doesn’t know 2FA is available on the site. Two-factor authentication is an extra layer of protection for your 1Password account. When turned on, a second factor will be required to sign in to your account on a new device, in addition to your Master Password and Secret Key. Learn more about authentication and encryption in the 1Password security model. (2FA, Watchtower, Desktop client) You might wonder 'why the hell would this guy choose Dashlane over 1Password if his main problem was the price?' But the reason is simple. In some countries, it seems like Dashlane price is relatively very low (I had to pay about 0.99USD per month). 1Password Family recover with 2FA If I recover an account that has 2FA enabled, during the recovery phase (choice of new master password, generation of a new secret key, etc) is 2FA disabled or will the recovered user have to enter his old 2FA? What 1Password offers is greater convenience. Since 1Password already runs securely on Mac and iOS devices, you can have access to your 2FA codes on any of your Mac and iOS devices without having to mess around with Bluetooth (which means that it will work on any Mac, even ones without Bluetooth 4.0).
You are one data breach away from having your entire online life turned upside down. The problem is passwords, which are hopelessly fragile ways to secure valuable resources.
Don't be lulled into a false sense of security by the belief that creating a longer, more complex, harder-to-guess password will somehow make you safer online. You can create a password that is so long and complex it takes you five minutes to type, and it will do nothing to protect you if the service where you use that password stores it improperly and then has their server breached. It regularly happens.
Also: Best VPNs • Best security keys• Best antivirus
zdnet recommends
Everyone needs a password manager. It's the only way to maintain unique, hard-to-guess credentials for every secure site you and your team access daily.
And even with reasonable policies in place (complexity, changed regularly, not reused), people are still the weakest link in the security chain. Social engineering can convince even intelligent people to enter their credentials on a phishing site or give them up over the phone.
The solution is two-factor authentication, or 2FA. (Some services, being sticklers for detail, call it multi-factor authentication or two-step verification, but 2FA is the most widely used term, so that's the nomenclature I've chosen to use here.)
A 2019 report from Microsoft concluded that 2FA works, blocking 99.9% of automated attacks. If a service provider supports multi-factor authentication, Microsoft recommends using it, even if it's as simple as SMS-based one-time passwords. A separate 2019 report from Google offered similar conclusions.
In this article, I answer some of the most common questions people ask me about 2FA.

How does 2FA work? Isn't it inconvenient?
Turning on 2FA for a service changes the security requirements, forcing you to provide at least two proofs of identity when accessing a secure service for the first time on an unknown device. After you successfully meet that challenge, you usually have the option to categorize the device as trusted, which means that 2FA requests should be relatively rare on the devices you use regularly.
Those two forms of authentication can come from any combination of at least two of the following elements:
- 'Something you know,' such as a password or PIN
- 'Something you are,' such as a fingerprint or other biometric ID
- 'Something you have,' such as a trusted smartphone that can generate or receive confirmation codes, or a hardware-based security device
For the most part, the two-factor authentication systems you see in place today use the first item (your password) and the last item (your smartphone). Smartphones have become ubiquitous, making them ideal security devices.
Your smartphone can assist with authentication by providing a unique code that you use along with your password to sign in. You can acquire that code in one of two ways: Sent as a text message from the service, or generated by an app installed on your phone.
Here, for example, is what I saw moments ago when I tried to sign in to my Gmail account from a browser I had never used before.
© Provided by ZDNet If someone tries to sign in to an account protected by 2FA, they'll need a second proof, such as the code from an authenticator appIf this sign-in request were from someone who had stolen my Google account credentials, they'd be stopped dead in their tracks. Without that code, they can't continue the sign-in process.
Most (but not all) services that support 2FA offer a choice of authentication methods. Google and Microsoft, for example, can both push notifications to a trusted device; you tap the notification to approve the sign-in. An increasing number of services support the use of hardware security keys (see: 'YubiKey hands-on: Hardware-based 2FA is more secure, but watch out for these gotchas.')
And, of course, most services offer the option to print out backup recovery codes, which you can store in a safe place and use in the event your usual secondary authentication method is unavailable. If your smartphone is lost, stolen, or damaged, you'll need those codes.
ZDNet Recommends
While robust passwords go a long way to securing your valuable online accounts, hardware-based two-factor authentication takes that security to the next level.
Which authentication method is best?
The best authentication method is the one you're most comfortable with. Just make sure you have at least two options, to avoid the risk of being locked out of your account.
I prefer the option to use an authenticator app rather than receiving codes via text message whenever possible, and so should you, for two good reasons. The first is a matter of simple logistics. There are times when you have access to the internet (via a wired connection or Wi-Fi) but can't receive a text message, because your cellular signal is weak or nonexistent, or you're using a different SIM while traveling. The second is the small but real chance that an attacker will social-engineer their way through your mobile carrier's defenses to acquire a SIM card with your phone number, a process called 'SIM-jacking.'
The most popular 2FA app is Google Authenticator, which is available on iOS and Android. But there are plenty of alternatives; because the process for generating secure tokens is based on open standards, anyone can write an authenticator app that performs the same function. In fact, you can use multiple authenticator apps. I use Microsoft Authenticator, which is capable of receiving push notifications from personal and business accounts on Microsoft's platforms, as well as 1Password, which integrates 2FA support into the same app that manages passwords, making sign-in even more seamless. I almost recommend the third-party app Authy, which allows you to manage authenticator codes on multiple devices with the ability to back up and restore account settings. (For details, see 'Protect yourself: How to choose the right two-factor authenticator app.')
It's worth noting that setting up an account in your authenticator app only requires a data connection during the initial configuration. After that, everything happens on your device. The process is governed by a well-accepted standard that uses the Time-based One-Time Password algorithm (TOTP). That algorithm uses the authenticator app as a sophisticated calculator that generates codes using the current time on your device and the shared secret. The online service uses the same secret and its own timestamp to generate codes that it compares against your entry. Both sides of the connection can adjust for timezones without problem, although your codes will fail if the time on your device is wrong.
How do I know which services support 2FA?
When I started writing about this technology a decade ago, 2FA support was relatively rare. Today, it's commonplace.
Security
Simple steps can make the difference between losing your online accounts or maintaining what is now a precious commodity: Your privacy.
Google accounts, including both consumer Gmail and business GSuite accounts, offer a wide range of two-step verification alternatives. All Microsoft accounts, including the free accounts used with Outlook.com, Xbox, Skype, and other consumer services, support a variety of authentication options, as do the Azure Active Directory accounts used with Microsoft's business and enterprise services, including Microsoft 365 and Office 365.
2FA support is ubiquitous among social media services (Facebook, Twitter, Instagram, and so on). Every online storage service worth considering supports 2FA, as do most domain registrars and web hosting companies. If you're unsure about a specific service, the best place to check is a superb open source information repository called the Two Factor Auth List. And if a high-value service you rely on doesn't support 2FA, well, maybe you should consider switching to one that does.
Which services should I protect first?
You probably have login credentials at dozens of online services that support 2FA, so the best strategy is to make a prioritized list and work your way through it. I suggest these priorities:
- Password/identity managers. Using a password manager is perhaps the most important way to ensure that you have a strong, unique password for every service, but that also creates a single point of attack. Adding 2FA shores up that potential weakness. Note that for some password management software, 2FA support is a paid option.
- Microsoft and Google accounts. If you use services from either company, adding 2FA support is essential. Fortunately, it's also easy.
- Email accounts. If a bad actor can take over your email account, they can often wreak havoc, because email messages are a standard means of sending password reset links. Messages sent from a compromised email account can also be used to attack your friends and co-workers (by sending malware-laden attachments, for example). If you use Outlook.com, Exchange Online, Gmail, or G Suite, your email account uses the identity verification method associated with your Microsoft or Google account. If you use a different email service, you'll need to set up 2FA separately.
- Social media accounts. As with email, the biggest risk associated with a hacked Twitter or Facebook account is that it will be used against your friends and associates. Even if you're a lurker who rarely posts anything on social media, you should protect these accounts.
- Banks and financial institutions. Most banks and credit card companies have made significant investments in back-end fraud detection programs, which is why 2FA options are typically limited compared with other categories. Nonetheless, it's worth exploring these settings and tightening them as much as possible.
- Shopping and online commerce. Any site where you've saved a credit card number should be secured.
How do I set up 2FA?
Setting up additional security for most online services requires minimal technical skills. If you can use your smartphone's camera, type a six-digit number, and tap OK in a dialog box, you have all the skills required. Logic pro 10 free download for mac. The most difficult part of the job is finding the page that has the relevant settings.
If you're using SMS messages, all you need to do is associate a mobile phone number with your account. (You can also use a virtual phone line, such as a Google Voice number, that can receive SMS messages.) Configure the account to send a code to that number whenever you sign in on an untrusted device. For example, here's what this option looks like when enabled on a Twitter account:
© Provided by ZDNet The simplest 2FA option is a code, sent via SMS message to a registered phone. This is the 2FA setup page for Twitter.Setting up 2FA on a Twitter account requires you to first re-enter your password and then enter the phone number where you want to receive authentication codes. After you complete that process, you'll receive a code on that device. Enter the code to confirm you received it, and the 2FA setup is complete. Helpfully, Twitter automatically generates a recovery code at the end of this setup process; print it out and file it in a safe place so you can recover in the event your primary 2FA method no longer works.
To get started with an authenticator app, you first need to install the app on the mobile device you want to use as your second authentication factor:
- If you carry an iOS device, you can get the Google Authenticator app from the App Store. (It's optimized for use on iPhones but should work on an iPad as well.) On Android devices, install the Google Authenticator app from the Google Play Store.
- The Microsoft Authenticator app, which uses the same standard to create authentication tokens, is available for Android devices from the Google Play Store and for iOS devices from the App Store.
- Authy is also available from the App Store and from the Google Play Store.
- If you use the LastPass password manager, consider installing the LastPass Authenticator app, which is designed to work with the LastPass app on mobile devices and the desktop.
- If you use 1Password as your password manager, 2FA support is built into the 1Password app on all platforms. For details on how to use the One-Time Password feature, see this 1Password support page.
After you install the app for your device, the next step is to set it up to work with each account where you have enabled 2FA.
Also: Make your cloud safer: How to enable two-factor authentication for the most popular cloud services.
The setup process typically requires that you enter a shared secret (a long text string) using the mobile app. All of the mobile apps I listed above support using a smartphone camera to take a picture of a QR code, which contains the shared secret for your account. That's much easier than entering a complex alphanumeric string manually.
Here, for example, is the QR code you'll see when setting up a Dropbox account:
© Provided by ZDNet In your smartphone app, choose the option to add a new account and then snap a picture of the bar code to automatically set up 2FA support.In your authenticator app. choose the option to add a new account, choose the bar code option, aim the smartphone at the bar code on your computer screen, and wait for the app to fill in the necessary fields.
After you set up the account in the authenticator app, it begins generating codes based on the shared secret and the current time. To complete the setup process, enter the current code from the authenticator app.
The next time you try to sign in with a new device or web browser, you'll need to enter the current code, as displayed by the authenticator app.
If you use older email apps that don't support modern authentication with an account that's protected by 2FA, your normal password won't work anymore. You'll need to generate special passwords for use exclusively with those apps. The security settings for your account should guide you through that process. (But really, if you are using an old app that requires an app password, maybe you should consider replacing it.)
As part of the 2FA setup process, you should also generate one or more recovery codes, which you can print out and store in a safe place. In the event your smartphone is lost or damaged, you can use those codes to regain access to your account.
How do you transfer 2FA accounts to a new smartphone?
If you use SMS text messages as a second factor for authentication, transferring your number to the new phone will seamlessly transfer your 2FA setup too.
Some authenticator apps allow you to generate codes on multiple devices. 1Password and Authy both fall into this category. Set up the app on the new phone, install the app, sign in, and then check each account to confirm that the codes generated on the new phone work properly. Microsoft Authenticator allows you to back up codes to the cloud and restore them on a new device. For instructions, see 'Back up and recover account credentials using the Microsoft Authenticator app.'
For Google Authenticator and other no-frills apps, however, you'll need to manually re-create each account on the new device. Install the authenticator app on your new device and repeat the setup process for each account you used with your old phone. Setting up an account on a new authenticator app automatically disables codes generated by the old device.
Two-factor authentication will stop most casual attacks dead in their tracks. It's not perfect, though. A determined attacker who is directly targeting a specific account might be able to find ways to work around it, especially if he can hijack the email account used for recovery or redirect phone calls and SMS messages to a device he controls. But if someone is that determined to break into your account, you have a bigger problem.
Any questions? Send me a note or leave a comment below.
Security
Everywhere you go the number one advice you’ll get about securing an account is to use 2FA.
If you’re not aware, 2FA is two-factor authorization, also called two-step authorization. You either get a text message, email, or use an app that tells you what code to enter after your password. It’s like having a second password. Since the 2FA code continually changes, it’s not worth stealing, unlike a password.
I’m not going to argue that you’ll be better off without 2FA. Even the weakest of the 2FA, SMS text message, is still better than not having 2FA.
My issue with 2FA is that people forget the whole point of it and why we use it in the first place. There are also undesirable consequences of blindly pushing 2FA that are destroying its effectiveness and making some people less secure.
What’s The Point of 2FA?
The whole point of 2FA is if your 1FA (your password) is already known.
If you never reuse passwords, it makes 2FA pointless. Well, I guess a better word would be redundant.
Think of it like this – you have two locks on your door, one lock has a PIN and the other requires a Key (something you know and something you have). The PIN is like your password and the Key is your 2FA app. Where a lot of people go wrong is reusing passwords with their 2FA app. This would be like putting a sticky note with the PIN code next to the first lock – this is defeating the whole point of having two locks.
Most people don’t realize this issue and think since they have 2FA they’ll be fine which brings me to my first gripe with 2FA.
2FA Encourages Password Reuse
People are bad about reusing passwords. If you stop reusing passwords, you will prevent most, if not all, hacking attempts. Keyword being “most.”
When someone is “hacked,” the first thing to come out of people’s mouth is to turn on 2FA. While it will stop unauthorized access, it’s not solving the real problem.
The real problem is that they need to stop reusing passwords. Only turning on 2FA and doing nothing else is like jumping out of a plane knowing your first parachute will fail – who would do that?
If we blindly advise only turning on 2FA and doing nothing else the user will continue their path of reusing passwords.
Here is a great real example I’ve come across for this exact issue.
“I can’t stress how important 2FA is. I woke up to 56 requests from my authentication all because someone had been trying to get in.“Archive.Another one.
Here is another one that is also a great example of this
I’m sitting on break at work and I’m watching the “Authy” app just send me 2FA request notifications one after the other. Scary knowing somebody wants my account that bad. But glad knowing that 2FA is doing it’s job in protecting my account.If it’s said once it’s said a million times but please if you haven’t enable 2 factor authentication I promise you the effort you put in is well worth the pay off of having a secure account.Archive.
Another one. Archive.
These people were only ever told to turn on 2FA. No one told them to stop reusing passwords so they kept their bad password and still have hackers trying to get in. The problem is not solved because they’re getting multiple requests to log in. To a hacker seeing a screen requiring 2FA means the password works and the users reuses it so the hacker will move on to other sites to get in and steal what they need. And these poor people still have not solved their real issue of password reuse and now another account of there’s will get taken over where someone again will tell them to turn on 2FA and we repeat the vicious cycle til they get to a site that doesn’t have 2FA.
If we instead told them to give every account a unique password by using an app like a password manager, they would have solved the real issue and not use 2FA as a bandaid.
Plus, if we’re going to have people start to use 2FA apps, we might as well get them to use a password manager app first and solve the real issue. After addressing the underlying problem, they can then move on to hardening their accounts with 2FA.
2FA Doesn’t Make You Unhackable
2FA gets pushed as some magic cure to hacking.
That is false.
Here is the crazy part; someone could argue that some people are more hackable after enabling 2FA.
If you tell someone they can’t die because they now have this magic app, many will, unfortunately, believe you. They’ll start to do foolish things because they think they can’t get hurt.
This is how 2FA is being treated.
You start to drop your guard; you got 2FA now so no need to worry about getting hacked. Life is good! That is until you get a phishing page that steals your info.
And yes, 2FA can’t stop all phishing attacks.
Don’t believe me? Watch this video.
Hackers will send a phishing email that gets you to log in to what seems to be the legit site, that’s because it is. The hackers use a reverse proxy which acts more like a web browser.
They’re the middleman and once you login the site gives the “browser” a token so you (and now the hacker) can stay logged in. All this happens under a second, and since everyone made you think you’re safe because you have 2FA, you don’t pay any attention to the little things that are off. Once the hackers have the token, they don’t need your password or 2FA codes anymore. And yes, a VPN won’t protect you against this kind of attack.
2FA Doesn’t Stop Malware Attacks
Another point that gets overblown is that 2FA can protect you against malware.
This is not true either.
If your computer is infected, you’ve already lost the game; it’s not your computer anymore.
When the computer is infected, hackers can change how your computer responds to websites. If you go to Google.com, they could very easily change it to their phishing site and do the reverse proxy attack as I mentioned before.
Or they could steal the tokens already stored on your computer.
Another possibility is to use your computer as if they’re sitting in front of it. They have full access to the computer, and this is the holy grail for them. It’s much harder to dispute unauthorized charges if they’re coming from your computer.
A 2FA code that changes every 30 seconds won’t help you on a computer that is already infected. There are so many possibilities to get what they need that it doesn’t matter what you use. It’s like thinking you won’t explode on a minefield if you wear sandals – you’re playing a losing game no matter what you use.
Bruce Schneier agrees with me on this one.
2FA Won’t Help If The Service Gets Breached
If a website is already breached your password or 2FA won’t matter because they have full access anyway.
But this is not what they think when they say 2FA will protect you if a website gets breached.
This goes back to my point that 2FA encourages password reuse.
They’ve reused their password and think their other accounts will be fine because they have 2FA. What they forget is the other accounts that don’t have 2FA are now in trouble.
You never realize how many accounts you have until you get the email saying someone else has logged in and taken over that account. I used to think I had maybe 30 passwords; after I got my password manager, I slowly realized I had hundreds, and it still grows to this day.
Plus, reusing passwords because 2FA will save you is backwards thinking. Going back to my parachute metaphor, you don’t intentionally destroy the first parachute because the second one will save you. Why would you treat your online accounts this way?
The Other Drawback of 2FA
When talking about how great 2FA is the one thing people forget about is its biggest flaw.
You can turn off 2FA.
Here is one great real world example of the fact you can turn off 2FA…
Many services know customers will either lose their device with 2FA on it or do something where they can’t use it. So they’ll need a way to disable 2FA.
Some services like Apple do it the best by making users wait days, if not weeks, to turn it off after proving who they are.
Then there are far more services that do it all wrong and can turn it off with just an email or even worse answering some simple security question.
If all it took to turn off 2FA is knowing what high school you went to can we even claim 2FA is useful?
To give you an example, Steam allows you to turn off Steam Guard (2FA) so long as you know the password. If you can turn off 2FA just by simply knowing the 1FA (password) you never had 2FA; you instead had extra hoops to jump through to log in to your account.

It will always boil down to using a unique password for every account. A unique password is far more important than 2FA.
So… Should We Even Use 2FA?
Use 1password 2fa
Yes, you should still use 2FA, but there is an order you must follow.
Before you even think about 2FA, you need to solve the 1FA problem first.
Step 1 – Stop reusing passwords. Get a password manager and give every account a unique password no matter how unimportant you think it is.
Step 2 – After the first step, you can do 2-Step (2FA). Get it?!?!?!
2fa 1password Fortnite
When Step 1 is done and you have given every account a unique password you can move onto setting up 2FA. You should only use 2FA to further harden the security of the account.
1password 2fa Scanner Not Working
Never think of 2FA as protecting your account if your password is known but instead as more friction to logging into the account. The more friction you have the less desirable it becomes to steal.
Step 2.B – The fallback options a site has to turn off 2FA must also be considered. If all it takes to turn off 2FA is answering security questions should you bother with 2FA? If you have a genuinely unique password, I will argue it’s not worth having 2FA.
2fa 1password
Don’t forget if the fallback option is to email you, it would be wise to make sure that email account has 2FA on and its fallback options are not easy to get around either.
2fa 1password Extension
Others Agree
1password 2fa Lost Phone
A 2FA app is essentially a password manager. A 2FA seed/code is essentially a password. “Time-based” thing does not add any security, and 6-digits thing makes security even worse. 2FA is obscure, inconvenient, hard to backup, bruteforce-able password manager. You don’t need 2FA, all you need is a unique complex password and a password manager. https://sakurity.com/blog/2015/07/18/2fa.html
